Universal Cloud Storage Press Release: Most Recent Updates and Innovations
Universal Cloud Storage Press Release: Most Recent Updates and Innovations
Blog Article
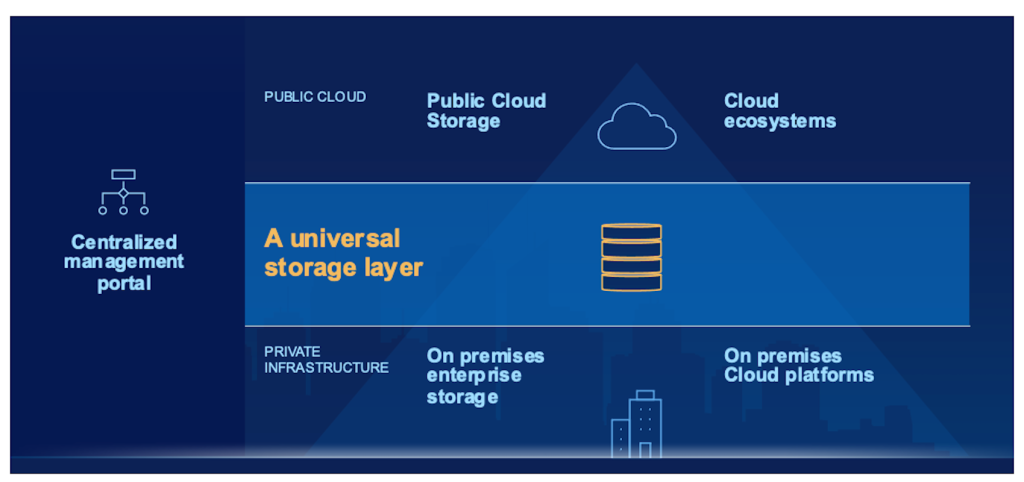
Discovering the Function of Universal Cloud Storage Space Solutions in Information Security and Conformity
As services significantly depend on cloud storage space solutions to handle and secure their information, discovering the detailed duty these solutions play in ensuring data safety and meeting regulative standards is vital. By diving right into the nuances of universal cloud storage services, a more clear understanding of their impact on data security and regulative conformity arises, shedding light on the intricacies and chances that exist in advance.
Value of Cloud Storage Space Provider
Cloud storage services play an essential role in contemporary information management methods because of their scalability, accessibility, and cost-effectiveness. With the rapid development of information in today's digital age, companies are significantly turning to cloud storage remedies to meet their advancing requirements. Scalability is an essential benefit of cloud storage, enabling organizations to quickly change their storage capacity as data requirements fluctuate. This adaptability makes sure that companies can successfully manage their information without the requirement for substantial ahead of time financial investments in equipment infrastructure.
Accessibility is one more vital aspect of cloud storage space services. By keeping data in the cloud, customers can access their info from anywhere with a web connection, helping with collaboration and remote job. This accessibility promotes operational efficiency and makes it possible for seamless sharing of information across teams and areas.
Moreover, the cost-effectiveness of cloud storage solutions can not be downplayed. By leveraging cloud storage space, services can lower expenditures related to investing in and maintaining physical web servers. universal cloud storage. In addition, many cloud storage carriers offer pay-as-you-go rates models, allowing companies to pay just for the storage space capacity they use. In general, the significance of cloud storage services lies in their capability to enhance data monitoring processes, boost access, and reduced functional expenses.
Information Security Strategies With Cloud
Applying durable data encryption procedures is vital for guaranteeing the safety and privacy of details stored in cloud atmospheres. Encryption plays a critical duty in guarding data both en route and at remainder. By encrypting information before it is submitted to the cloud and maintaining control over the encryption tricks, companies can protect against unauthorized access and minimize the risk of data breaches. In addition, applying gain access to controls and verification mechanisms assists in regulating that can access the information kept in the cloud. Multi-factor verification, solid password policies, and routine gain access to evaluations are some methods that can enhance data security in cloud storage solutions.
Routinely supporting data is one more crucial aspect of data defense in the cloud. By producing back-ups stored in separate areas, companies can make sure information availability and resilience in instance of unanticipated events such as cyber-attacks, equipment failures, or all-natural calamities. Carrying out routine protection audits and evaluations can help identify susceptabilities and make sure compliance with information protection guidelines. By incorporating encryption, accessibility controls, back-ups, and normal security evaluations, organizations can develop a durable data defense method in cloud atmospheres.
Conformity Considerations in Cloud Storage Space
Provided the crucial nature of information defense methods in cloud environments, organizations need to likewise focus on conformity considerations when it comes to saving data in the cloud. When making use of cloud storage solutions, companies require to ensure that the company conforms with industry-specific standards such as GDPR, HIPAA, or PCI DSS, depending on the kind of information being kept.
Obstacles and Solutions in Cloud Safety And Security
Ensuring durable safety actions in cloud atmospheres presents a diverse challenge for companies today. Among the primary difficulties in cloud protection is data breaches. Destructive stars regularly target cloud systems to acquire unapproved accessibility to delicate information. To minimize this threat, organizations need to execute solid encryption procedures, gain access to controls, and routine security audits. Another challenge is the shared obligation design in cloud computing, where both the cloud company and the consumer are in charge of various facets of security. This can result in confusion and spaces in safety and security coverage otherwise clearly defined. Organizations has to plainly lay out duties and duties to make certain thorough protection procedures are in location.
Future Patterns in Cloud Data Security
The evolving landscape of cloud information protection is noted by a growing emphasis on aggressive protection approaches and flexible safety and security procedures (universal cloud storage). As technology advancements and cyber hazards end up being a lot more innovative, organizations are progressively concentrating on anticipating analytics, expert system, and equipment discovering to improve their data defense capabilities in the cloud
Among the future trends in cloud information security is the assimilation of automation and orchestration devices to simplify safety operations and action processes. By automating routine jobs such as risk detection, occurrence feedback, and spot administration, organizations can enhance their general protection pose and far better shield their information in the cloud.
In addition, the adoption of a zero-trust safety and home security design is getting grip in the world of cloud information defense. This approach presumes that risks could be both exterior and internal, needing continual authentication and permission for all customers and devices accessing the cloud atmosphere. By implementing a zero-trust framework, organizations can decrease the risk of data breaches and unapproved access to delicate information saved in the cloud.
Verdict
Report this page